By Default Active Directory Adds New Computers To What Group
Breaking News Today
Apr 02, 2025 · 6 min read
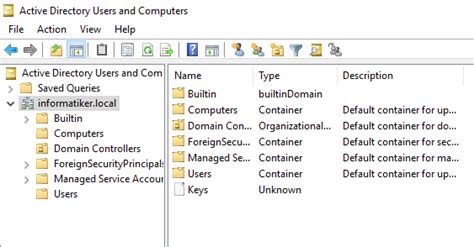
Table of Contents
By Default, Active Directory Adds New Computers to What Group? Understanding Default Group Membership in Active Directory
Active Directory (AD) is the cornerstone of many Windows-based networks, managing users, computers, and other resources. A crucial aspect of AD management involves understanding default group memberships. Knowing which groups new computers are automatically added to is fundamental for security planning, network administration, and troubleshooting. This article delves deep into the default group membership of computers joined to an Active Directory domain, explaining the implications and best practices.
The Default Group: Domain Computers
By default, when a computer joins a Windows Active Directory domain, it's automatically added to the Domain Computers group. This is the primary and most fundamental group membership for any domain-joined computer. The Domain Computers group is a built-in security group, meaning it's created automatically during domain creation and plays a critical role in managing access control.
Implications of Domain Computers Group Membership
Membership in the Domain Computers group grants the computer specific permissions and rights within the domain. These rights are crucial for the computer to function correctly within the network environment. These include, but aren't limited to:
-
Access to domain resources: The computer can access shared folders, printers, and other network resources that are accessible to members of the Domain Computers group. This is essential for day-to-day network operations.
-
Logon rights: The computer account has the necessary privileges to log on to domain controllers and other domain-joined servers. This is crucial for tasks like software updates, administrative tasks, and general network communication.
-
Group Policy application: Group Policies, which configure various settings and configurations on domain-joined computers, are applied based on group membership. Being a member of the Domain Computers group means the computer receives the default Group Policies applied to this group.
-
Security context: The Domain Computers group plays a key role in defining the security context for the computer. This impacts how the computer interacts with other resources and users within the domain, influencing access control lists (ACLs) and permissions.
Understanding the Security Implications
The Domain Computers group is a powerful group with inherent security implications. It’s crucial to understand that any changes made to permissions at the Domain Computers group level will affect all domain-joined computers. This is why careful consideration is essential when modifying the permissions assigned to this group.
Overly permissive settings can create vulnerabilities, potentially enabling malicious actors to exploit the group’s wide-ranging access to gain unauthorized control over domain resources. Conversely, overly restrictive settings can hinder the functioning of legitimate applications and services.
Other Default Group Memberships (Contextual and Conditional)
While the Domain Computers group is the most prominent default group, a computer's group memberships can extend beyond this, depending on various factors, including:
-
Operating System: The specific version of Windows running on the computer can influence its group membership. Some features and roles might add the computer to additional groups based on the OS version and features installed.
-
Computer Role: If the computer serves a specific role, like a domain controller, print server, or member of a particular workgroup, it might automatically join additional security groups relevant to that role. For example, domain controllers are members of several critical groups related to their functionality.
-
Organizational Unit (OU) Placement: The Organizational Unit (OU) within Active Directory where the computer object resides can influence its group membership through Group Policy settings. Specific OUs might have Group Policy Objects (GPOs) that add computers within those OUs to additional groups. This provides granular control over group memberships based on departmental needs or functional requirements.
-
Third-party applications: Some third-party applications might add the computer account to specific groups upon installation to ensure proper functioning. These applications often require specific permissions for their processes to run effectively.
It’s important to note that these additional group memberships aren't always default; they often depend on the specific configuration of the Active Directory environment and the systems within it. A thorough audit is necessary to fully understand the group memberships of all computers in a given domain.
Best Practices for Managing Default Group Memberships
While you can't change the default addition of a computer to the Domain Computers group, you can manage the security implications of this membership, and other conditionally added memberships, in several ways:
-
Regularly audit group memberships: Periodically review the group memberships of both the Domain Computers group and individual computer accounts to identify any unnecessary or potentially risky memberships. This helps identify and address security vulnerabilities and maintain the integrity of your network environment.
-
Principle of Least Privilege: Apply the principle of least privilege when assigning permissions to groups, including the Domain Computers group. This means granting only the necessary permissions to the group to perform its functions, minimizing potential impact from any compromise.
-
Effective use of Group Policy: Leverage Group Policy to manage user and computer accounts centrally. GPOs offer fine-grained control over security settings, allowing administrators to enforce consistent configurations and limit potential vulnerabilities across the domain.
-
Regular security updates: Keep all domain controllers and domain-joined computers updated with the latest security patches to protect against known vulnerabilities.
-
Strong password policies: Enforce strong password policies for all user and computer accounts to prevent unauthorized access.
-
Monitor security logs: Regularly monitor security logs for suspicious activities and anomalies to promptly detect and respond to security incidents.
-
Implement multi-factor authentication (MFA): MFA adds an additional layer of security, making it significantly more difficult for attackers to gain unauthorized access to domain resources, including computers.
Troubleshooting Common Issues Related to Default Group Membership
Understanding default group memberships is crucial for troubleshooting various issues. Problems can arise if a computer isn't correctly added to the Domain Computers group or if group permissions are misconfigured. Common problems include:
-
Access denied errors: If a computer cannot access network resources, it could be due to incorrect group membership or insufficient permissions within the Domain Computers group (or other relevant groups). Verify the computer's group membership and permissions.
-
Software installation failures: Some software might require specific permissions to install or run correctly. If the computer lacks these permissions, the software installation might fail. Check the software's requirements and the computer's group memberships to ensure it has the necessary permissions.
-
Group Policy issues: If Group Policy isn't applying correctly, the issue might be related to the computer's group membership or incorrect configuration of GPOs affecting that group. Review the GPOs applied to the Domain Computers group and verify their proper function.
-
Network connectivity problems: Incorrect group memberships or permissions can result in network connectivity issues, particularly when accessing shared resources. Verify the computer's network configuration and group memberships.
Conclusion: Proactive Management is Key
The default addition of computers to the Domain Computers group in Active Directory is a fundamental aspect of network management. Understanding the implications of this default membership and proactively managing group permissions are essential for maintaining a secure and efficient network. By employing best practices, regularly auditing group memberships, and addressing potential issues promptly, organizations can minimize risks and ensure smooth operation of their Active Directory environment. Remember that a well-planned and well-maintained Active Directory infrastructure is crucial for any organization relying on a Windows-based network. Regular review and proactive security measures are the foundation for a robust and secure environment.
Latest Posts
Latest Posts
-
Bach Created Masterpieces In Every Baroque Genre Except
Apr 03, 2025
-
A Defining Characteristic Of American Politics Is
Apr 03, 2025
-
Hardware Lab Simulation 7 1 Investigating Network Connection Settings
Apr 03, 2025
-
In Cell B9 Enter A Formula Using Npv
Apr 03, 2025
-
All Of The Following Are Roles Of Protein Except
Apr 03, 2025
Related Post
Thank you for visiting our website which covers about By Default Active Directory Adds New Computers To What Group . We hope the information provided has been useful to you. Feel free to contact us if you have any questions or need further assistance. See you next time and don't miss to bookmark.
