True Or False Clients Authenticate Directly Against The Radius Server
Breaking News Today
Apr 01, 2025 · 6 min read
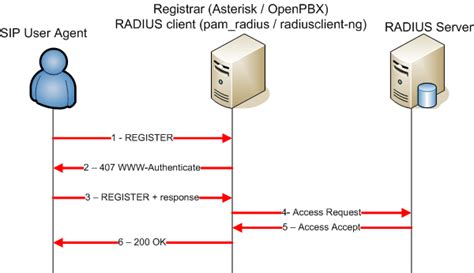
Table of Contents
True or False: Clients Authenticate Directly Against the RADIUS Server
The statement "Clients authenticate directly against the RADIUS server" is false. Clients don't directly authenticate with the RADIUS server. Instead, they authenticate with a network access server (NAS), which then acts as an intermediary to the RADIUS server for authentication, authorization, and accounting (AAA). Let's delve deeper into this crucial aspect of network security and explore the intricacies of the RADIUS protocol.
Understanding the RADIUS Protocol and its Components
RADIUS (Remote Authentication Dial-In User Service) is a networking protocol that provides centralized authentication, authorization, and accounting management for users connecting to a network. It's a cornerstone of network security, ensuring that only authorized users can access network resources. The protocol operates based on a client-server model, but the client isn't the end-user device. The key players are:
1. The Network Access Server (NAS): The Client's Gateway
The NAS is the client in the RADIUS client-server model. This is often a device like a router, switch, wireless access point (WAP), VPN gateway, or other network infrastructure component that initially receives the authentication request from a user's device (e.g., a laptop, smartphone, IoT device). The NAS acts as the gatekeeper, verifying the user's credentials before granting network access. It's crucial to understand that the NAS doesn't independently validate the user's identity; it forwards the request to the RADIUS server.
2. The RADIUS Server: The Authentication Authority
The RADIUS server is the central authentication server. It holds the user's credentials (username and password, or other authentication methods like certificates or tokens) and authorization policies. When the NAS forwards an authentication request, the RADIUS server verifies the credentials against its database. Based on the authentication result, it sends an authorization response back to the NAS, granting or denying access.
3. The User Device (Client): The Initiator of the Process
The user's device (e.g., a laptop, smartphone) is the entity initiating the connection to the network. It sends its authentication request to the NAS, but it never directly communicates with the RADIUS server. This direct communication is intentionally avoided for security reasons, centralizing authentication management and protecting the RADIUS server from direct exposure to potentially malicious clients.
The Authentication Process: A Step-by-Step Breakdown
Let's walk through the typical steps involved in the RADIUS authentication process:
-
Connection Request: A user attempts to connect to the network using their device. The device initiates a connection request to the NAS.
-
Access-Request to RADIUS Server: The NAS, receiving the connection request, prepares an Access-Request message containing the user's credentials (username, password) and other relevant information like the user's IP address, device type, and requested service. This message is then sent to the RADIUS server.
-
Authentication and Authorization: The RADIUS server receives the Access-Request and verifies the user's credentials against its database. If the credentials are valid, the server performs authorization checks, determining which network resources the user is permitted to access based on pre-defined policies.
-
Access-Accept or Access-Reject: Based on the authentication and authorization results, the RADIUS server sends an Access-Accept or Access-Reject message back to the NAS.
-
Network Access Granted or Denied: The NAS receives the response from the RADIUS server. If it's an Access-Accept message, the NAS grants the user network access. If it's an Access-Reject, the NAS denies the connection.
-
Accounting: Throughout the session, the NAS periodically sends accounting updates to the RADIUS server, recording the user's activity, connection time, and consumed resources. This information is essential for auditing, billing, and resource management.
Why Direct Authentication is Avoided
The design of RADIUS specifically avoids direct client authentication for several crucial reasons:
-
Security: Exposing the RADIUS server directly to clients increases its vulnerability to attack. By having the NAS act as an intermediary, the RADIUS server is shielded from various threats, including denial-of-service attacks and credential harvesting attempts.
-
Centralized Management: RADIUS allows for centralized management of authentication and authorization policies. Instead of configuring authentication on every individual NAS, administrators can manage all authentication settings from a single RADIUS server. This simplifies administration and ensures consistency across the entire network.
-
Scalability: The RADIUS architecture is scalable, accommodating the addition of new NAS devices and users without significant performance impacts. The central RADIUS server manages authentication for numerous clients, improving efficiency and reducing administrative overhead.
-
Flexibility: RADIUS supports various authentication methods, including passwords, certificates, tokens, and even multi-factor authentication. This flexibility allows organizations to adapt to their security needs and leverage the most suitable authentication mechanisms.
Security Implications of Misunderstanding RADIUS Authentication
A common misconception about RADIUS is that clients directly interact with the RADIUS server. This misunderstanding can lead to vulnerabilities and security weaknesses. For example:
-
Weak NAS Security: If the NAS is not properly secured, it can become a point of entry for attackers to bypass RADIUS security measures. A compromised NAS could relay malicious requests to the RADIUS server or directly access user data.
-
Misconfigured RADIUS Server: Incorrectly configuring the RADIUS server can expose it to vulnerabilities. For example, weak passwords, improper access controls, and outdated software can all compromise the security of the entire system.
-
Lack of proper auditing: Without robust accounting mechanisms within the RADIUS system, tracking and identifying malicious activity can become very challenging. The accounting component is crucial for detecting and responding to security breaches.
Advanced RADIUS Concepts and Considerations
-
RADIUS Extensions: RADIUS supports various extensions for advanced features, such as dynamic IP address assignment, Quality of Service (QoS) policies, and support for different authentication protocols.
-
Multi-Factor Authentication (MFA): RADIUS can be integrated with MFA systems to enhance security. This typically involves requiring users to provide multiple forms of authentication (e.g., password and one-time code) to gain access.
-
RADIUS Accounting: Accounting provides detailed logs of user activity. This data is crucial for auditing, billing, and capacity planning. It allows network administrators to monitor usage patterns, identify potential issues, and maintain network security.
-
RADIUS Federated Authentication: RADIUS can support federated authentication, allowing users to authenticate using their credentials from another organization's identity provider.
-
Integration with other systems: RADIUS can often be integrated with other security and network management systems, enabling comprehensive security and monitoring.
Conclusion
In conclusion, the assertion that clients directly authenticate against the RADIUS server is demonstrably false. The RADIUS architecture uses a network access server (NAS) as an intermediary, protecting the RADIUS server from direct client interactions and enhancing overall network security. Understanding the roles of each component – the NAS, the RADIUS server, and the user's device – is critical for maintaining a secure and efficient network. Properly securing the NAS, appropriately configuring the RADIUS server, and diligently monitoring the system’s activity are all vital practices to prevent security breaches. The implementation of robust RADIUS infrastructure, coupled with a strong understanding of its functionality, forms a critical component of a modern organization's overall security posture. Ignoring these aspects can expose your network to significant risks. Remember, security is a layered approach, and RADIUS, while vital, is only one piece of the puzzle.
Latest Posts
Latest Posts
-
Bach Created Masterpieces In Every Baroque Genre Except
Apr 03, 2025
-
A Defining Characteristic Of American Politics Is
Apr 03, 2025
-
Hardware Lab Simulation 7 1 Investigating Network Connection Settings
Apr 03, 2025
-
In Cell B9 Enter A Formula Using Npv
Apr 03, 2025
-
All Of The Following Are Roles Of Protein Except
Apr 03, 2025
Related Post
Thank you for visiting our website which covers about True Or False Clients Authenticate Directly Against The Radius Server . We hope the information provided has been useful to you. Feel free to contact us if you have any questions or need further assistance. See you next time and don't miss to bookmark.
