What Is The Password For The Companyinfo Zip Hash
Breaking News Today
Apr 03, 2025 · 4 min read
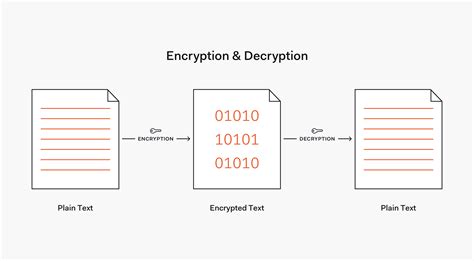
Table of Contents
What is the Password for the companyinfo.zip Hash? A Comprehensive Guide to Data Security and Ethical Hacking
The question, "What is the password for the companyinfo.zip hash?" is inherently problematic. It directly implies an attempt to access data without authorization, a serious breach of ethical conduct and potentially illegal activity. This article will not provide the password, as doing so would be irresponsible and harmful. Instead, we'll explore the broader context of data security, password protection, and ethical considerations surrounding unauthorized access attempts. Understanding these principles is crucial for protecting sensitive information and navigating the digital landscape responsibly.
Understanding Hashing and Password Security
A hash is a one-way function that transforms data (like a password) into a seemingly random string of characters. This process is irreversible; you cannot retrieve the original password from its hash. This is a cornerstone of password security. When you enter a password, the system doesn't store the password itself but rather its hash. If someone gains access to the database, they only have the hashes, not the actual passwords.
The security of this system depends on the strength of the hashing algorithm and the length and complexity of the passwords. Weak hashing algorithms are vulnerable to cracking, while short, simple passwords are easily brute-forced (tried repeatedly until guessed).
Why you should NEVER try to crack a password:
- It's illegal: Unauthorized access to computer systems and data is a crime punishable by law, with potentially severe consequences including hefty fines and imprisonment.
- It's unethical: Violating someone's privacy and stealing their data is a morally reprehensible act. Respect for privacy and data security is paramount.
- It's risky: Attempting to crack passwords can expose you to malware, viruses, and other cyber threats. You risk infecting your own system.
- It's often futile: Modern hashing algorithms and password protection measures make cracking passwords extremely difficult, especially without specialized tools and expertise.
The Importance of Strong Passwords
The best defense against unauthorized access is a strong, unique password. Here's what makes a strong password:
- Length: Aim for at least 12 characters, preferably longer.
- Complexity: Use a combination of uppercase and lowercase letters, numbers, and symbols. Avoid easily guessable patterns.
- Uniqueness: Never reuse passwords across different accounts. If one account is compromised, others remain safe.
- Password Managers: Use a reputable password manager to securely generate and store strong, unique passwords for all your online accounts. This significantly simplifies password management without compromising security.
Ethical Hacking and Penetration Testing
Ethical hacking, also known as penetration testing, involves simulating real-world cyberattacks to identify vulnerabilities in a system. This is done with the explicit permission of the system owner to improve security. Ethical hackers employ various techniques, but they adhere strictly to ethical guidelines and legal frameworks. Attempting to crack a password without permission is NOT ethical hacking.
Key differences between ethical hacking and unauthorized access:
| Feature | Ethical Hacking | Unauthorized Access |
|---|---|---|
| Authorization | Explicit permission from the system owner | No permission; illegal and unethical |
| Intent | Identify vulnerabilities to improve security | Steal data, cause damage, or gain control |
| Legality | Legal and ethical when done properly | Illegal and unethical |
| Methodology | Follows ethical guidelines and legal frameworks | Uses any means necessary to gain access |
Alternative Approaches to Accessing Data
If you legitimately need to access the data within companyinfo.zip, here are some appropriate steps:
- Contact the data owner: If you are an employee, contact your IT department or supervisor. If you're a client, contact the company's support team.
- Use proper authentication methods: If you have legitimate access, log in using the correct credentials provided to you.
- Seek legal counsel: If you believe you have a legal right to access the data, consult with a lawyer.
Data Security Best Practices
Strong passwords are only part of the equation. Organizations and individuals should implement robust data security measures:
- Regular software updates: Keep all software up-to-date to patch security vulnerabilities.
- Strong firewalls: Protect networks from unauthorized access.
- Antivirus and anti-malware software: Detect and remove malicious software.
- Data encryption: Encrypt sensitive data both in transit and at rest.
- Access control: Implement strict access controls to limit who can access specific data.
- Regular security audits: Conduct regular security assessments to identify weaknesses.
- Employee training: Educate employees about security best practices.
- Incident response plan: Have a plan in place to respond to security breaches.
Conclusion
The pursuit of the password for companyinfo.zip without proper authorization is fundamentally unethical and illegal. This article emphasizes the importance of respecting data security, adhering to ethical principles, and utilizing appropriate methods for accessing information. Instead of seeking unauthorized access, focus on building a robust security posture and utilizing ethical and legal means to obtain access to data when needed. Remember, data security is a shared responsibility, and proactive measures are crucial in preventing data breaches and protecting sensitive information. Prioritizing ethical conduct and responsible digital citizenship is paramount in today's interconnected world.
Latest Posts
Latest Posts
-
Which Of The Following Statements Best Defines Maneuvers
Apr 04, 2025
-
Which Of The Following Statements Is True Of Teratogens
Apr 04, 2025
-
In What Sense Are Telescopes Like Time Machines
Apr 04, 2025
-
Kurt And Mitch Visit An Amish Village
Apr 04, 2025
-
Which Section Of The Package Insert Lists Any Cancer Risks
Apr 04, 2025
Related Post
Thank you for visiting our website which covers about What Is The Password For The Companyinfo Zip Hash . We hope the information provided has been useful to you. Feel free to contact us if you have any questions or need further assistance. See you next time and don't miss to bookmark.
