Which Of The Following Poses A Physical Security Risk
Breaking News Today
Mar 30, 2025 · 6 min read
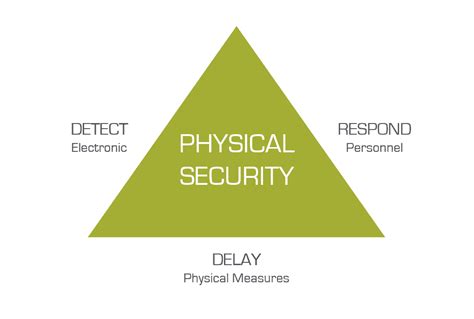
Table of Contents
- Which Of The Following Poses A Physical Security Risk
- Table of Contents
- Which of the Following Poses a Physical Security Risk? A Comprehensive Guide
- Defining Physical Security Risks
- Categorizing Physical Security Risks
- 1. Unauthorized Access & Intrusion
- 2. Theft & Vandalism
- 3. Sabotage & Terrorism
- 4. Natural Disasters & Environmental Threats
- 5. Insider Threats
- 6. Equipment Failure & Malfunction
- Assessing Specific Scenarios
- Conclusion: Proactive Physical Security Management
- Latest Posts
- Latest Posts
- Related Post
Which of the Following Poses a Physical Security Risk? A Comprehensive Guide
Physical security threats are a pervasive concern for individuals, businesses, and governments alike. Understanding these threats is the first step towards mitigating risk and ensuring safety. This comprehensive guide explores a range of potential physical security risks, examining their impact and providing strategies for prevention and response. We'll delve into various scenarios and assess their potential to compromise physical security.
Defining Physical Security Risks
Before examining specific examples, let's establish a clear definition. Physical security risks encompass any potential threat or vulnerability that could lead to unauthorized access, damage, theft, or harm to physical assets, personnel, or information. These threats can stem from both internal and external sources, and their impact can range from minor inconvenience to catastrophic loss.
Categorizing Physical Security Risks
We can broadly categorize physical security risks into several key areas:
1. Unauthorized Access & Intrusion
This is perhaps the most common physical security risk. It encompasses any situation where an unauthorized individual gains access to a protected area, facility, or system. This can include:
- Trespassing: Unauthorized entry onto private property. This could range from a casual wanderer to a deliberate intruder with malicious intent.
- Burglary: Forced or unauthorized entry with the intention of theft. This often involves breaking and entering, targeting valuable assets or sensitive information.
- Tailgating: Following an authorized individual through a secured entrance without proper identification or authorization.
- Shoulder surfing: Observing someone's actions, such as entering a PIN or password, to gain unauthorized access.
- Eavesdropping: Secretly listening to conversations to obtain confidential information.
Mitigating Unauthorized Access: Robust access control measures are essential. This includes security personnel, surveillance systems (CCTV), robust locking mechanisms, alarm systems, and access control systems (ACS) such as key card readers or biometric scanners. Regular security audits and employee training are crucial for maintaining a strong defense against unauthorized access.
2. Theft & Vandalism
Theft and vandalism represent significant physical security threats, resulting in financial losses, disruption of operations, and potential damage to reputation.
- Theft: The illegal taking of property, which can range from petty theft of small items to large-scale organized crime targeting high-value assets.
- Vandalism: Intentional destruction or damage to property, often driven by malicious intent, but also sometimes occurring randomly.
Mitigating Theft & Vandalism: Implementing robust security measures is paramount. This includes secure storage for valuable items, improved lighting, regular patrols, and the use of security cameras to deter and detect criminal activity. Installing alarm systems and utilizing tracking devices for valuable equipment can help in recovery efforts. Investing in strong and visible security systems acts as a powerful deterrent.
3. Sabotage & Terrorism
These represent extreme threats with potentially devastating consequences.
- Sabotage: Intentional damage or destruction of property or systems, often aimed at disrupting operations or causing harm.
- Terrorism: Acts of violence or threat of violence intended to intimidate or coerce a government or civilian population. This can manifest in various forms, including bombings, armed attacks, or cyberattacks targeting critical infrastructure.
Mitigating Sabotage & Terrorism: Addressing these threats requires a multi-layered approach, involving advanced security technologies, robust emergency response plans, and collaboration with law enforcement agencies. Thorough risk assessments, vulnerability analysis, and continuous monitoring of potential threats are vital for proactive risk mitigation.
4. Natural Disasters & Environmental Threats
Physical security is not solely about human threats; natural events can also pose significant risks.
- Earthquakes: Can cause widespread damage to buildings and infrastructure, leading to disruption and potential loss of life.
- Floods: Can inundate facilities, damaging equipment and disrupting operations.
- Fires: Can quickly spread, causing significant damage and putting lives at risk.
- Severe weather: Storms, hurricanes, and tornadoes can cause significant damage and disruption.
Mitigating Natural Disasters: Building resilience is key. This includes designing structures to withstand natural events, implementing robust backup systems and disaster recovery plans, and ensuring adequate insurance coverage. Regular inspections and maintenance of critical infrastructure are also crucial.
5. Insider Threats
These threats originate from within an organization. They are often more difficult to detect and mitigate than external threats.
- Malicious insiders: Employees or contractors who intentionally cause harm to the organization. This can involve theft of intellectual property, sabotage, or data breaches.
- Negligent insiders: Employees who unintentionally compromise security through carelessness or lack of training. This can lead to data breaches, accidental damage, or security vulnerabilities.
Mitigating Insider Threats: Strong background checks, thorough employee training on security protocols, access control measures based on the principle of least privilege, regular security audits, and robust monitoring systems are crucial for mitigating insider threats. A strong security culture within the organization is essential.
6. Equipment Failure & Malfunction
While not always considered a security threat in the traditional sense, equipment failure can create significant vulnerabilities.
- Security system malfunctions: Failures in surveillance systems, access control systems, or alarm systems can leave facilities vulnerable to intrusion or theft.
- Power outages: Can disrupt operations and disable security systems, leaving facilities vulnerable.
- Network failures: Can compromise communication and data access, impacting business continuity and security.
Mitigating Equipment Failure: Regular maintenance, redundancy systems (backup power generators, redundant network connections), and rigorous testing of security systems are essential to mitigate the risks associated with equipment failure.
Assessing Specific Scenarios
Let's consider some specific scenarios and analyze their physical security implications:
Scenario 1: An unlocked office door after hours. This clearly presents a significant physical security risk. Unauthorized individuals could easily gain access, potentially leading to theft, vandalism, or data breaches. This highlights the importance of proper locking procedures and security systems.
Scenario 2: A disgruntled employee with access to sensitive information. This represents a significant insider threat. The employee could potentially steal or leak confidential data, sabotage systems, or cause other harm. This underscores the need for robust background checks, employee monitoring, and strong access control policies.
Scenario 3: A lack of surveillance cameras in a high-traffic area. This creates a blind spot in security coverage, making the area vulnerable to various threats, including theft, vandalism, and even more serious crimes. The absence of surveillance makes it easier for perpetrators to act undetected. The strategic placement of surveillance cameras is a crucial element in physical security.
Scenario 4: Inadequate lighting in a parking lot. This increases the risk of crime, as poorly lit areas provide cover for criminals and make it more difficult for potential victims to see and avoid threats. Improved lighting significantly enhances safety and security.
Scenario 5: A failure of the fire alarm system during a fire. This could have catastrophic consequences, potentially leading to significant property damage, injuries, or even fatalities. Regular testing and maintenance of fire alarm systems are essential to ensure functionality and prevent such scenarios.
Scenario 6: A cyberattack targeting a building's access control system. While not strictly a "physical" security risk in the traditional sense, a successful cyberattack could render physical security measures ineffective, opening doors for physical intrusion. This emphasizes the interconnectedness of physical and cybersecurity.
Conclusion: Proactive Physical Security Management
Physical security is a multifaceted challenge requiring a proactive and holistic approach. By understanding the range of potential risks, implementing appropriate preventive measures, and developing robust response plans, organizations and individuals can significantly reduce their vulnerability and ensure a safer environment. Regular security assessments, employee training, and continuous improvement are vital for maintaining effective physical security. The consequences of neglecting physical security can be severe, impacting not only financial assets but also the safety and well-being of personnel. Therefore, a commitment to comprehensive physical security measures is a crucial investment in protection and peace of mind.
Latest Posts
Latest Posts
-
What Are The 3 S In The As K Model
Apr 03, 2025
-
What Is The Name Of The Ionic Compound Cao
Apr 03, 2025
-
Ben Is Asked To Memorize The Words Canine
Apr 03, 2025
-
Which Is Not An Aspect Of Being A Team Player
Apr 03, 2025
-
Letrs Unit 1 Session 6 Check For Understanding
Apr 03, 2025
Related Post
Thank you for visiting our website which covers about Which Of The Following Poses A Physical Security Risk . We hope the information provided has been useful to you. Feel free to contact us if you have any questions or need further assistance. See you next time and don't miss to bookmark.
